This robotic installation will steal and share your data — with your help.
The brainchild of ECAL student Martin Hertig, Sensible Data is a unique project designed to show just how easily people are willing to give up their personal information in exchange for fun. The playful installation collects a user’s data, judges their mood, age, gender and beauty, and creates a faux passport that is also randomly sent to another participant without them knowing.
If you think about, what really happens when you openly give your name, numbers and other information online, and where does it go? Although the experiment was done intentionally to test a small sampling’s confidence in how data is collected, it does highlight a much broader privacy issue that exists today, especially in the wake of several mainstream leaks.
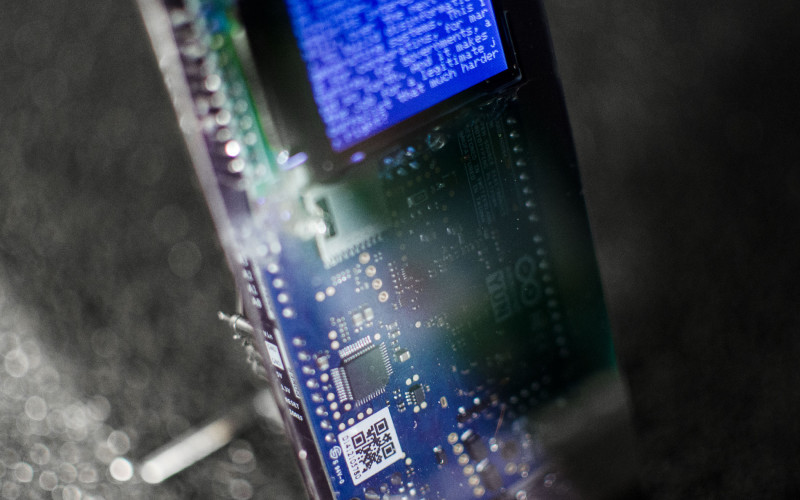
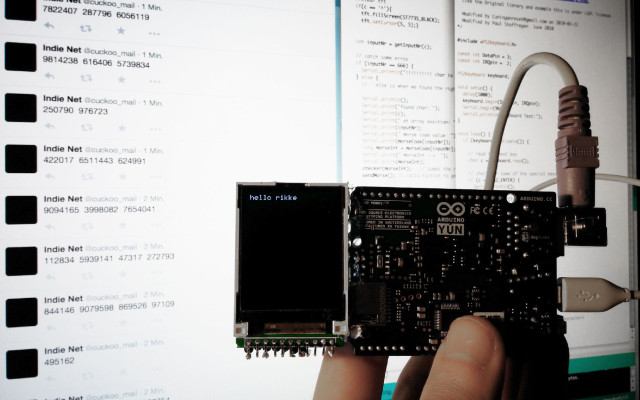
The Maker’s exploration is comprised of three machines that are essentially modified versions of the Piccolo CNC, an open source drawing device based on the Arduino Pro Micro (ATmega32U4). Meanwhile, a Raspberry Pi acts as the brain of the installation, running a Python script for every step of the process. Each script listens to the desired input and relays the plotting commands to the necessary gadget.
How it works is pretty straightforward. First, a participant snaps a selfie with an iPad that’s automatically synced up to a Raspberry Pi using Dropbox. A Python script takes this picture and converts it into a line drawing with the help of OpenCV. The user is then prompted to send a blank email to the project’s iCloud address.
From there, the person’s face is analyzed. Upon receiving an email, the Raspberry Pi transmits the previously taken image to the Rekognition API. The facial recognition program is able to properly determine one’s mood, age, gender and their beauty, which is measured as a percentage. This information is stored in a database and inked onto the novelty passport letter by letter using a laser-cut stamp-wheel.
Last but not least, the participant is asked to press a dubious button that is actually a fingerprint scanner. Once the validation step is complete, an email with a matching participant’s data including their fingerprint, photo and email address is sent to the user. (Absurdly, the matchmaking is determined by the amount of lines in the portrait.)
The idea is that, when encountered with a decision, more times than not people are willing to just hand over their likeness, not knowing what will be done with it. Intrigued? Check out the entire project here, and be sure to watch it in action below!